VMware has good documentation on setting up Hybrid Linked Mode in VMC, but the docs are a little bit confusing if all you want is Active Directory authentication into the VMC vCenter. This post shows how I was able to configure AD authentication for a VMC on AWS vCenter.
Update October 2023: If you do follow the instructions in this blog, there is an update about permissions that I wrote this month: vCenter Roles with LDAP credentials in VMware Cloud on AWS
Step 1
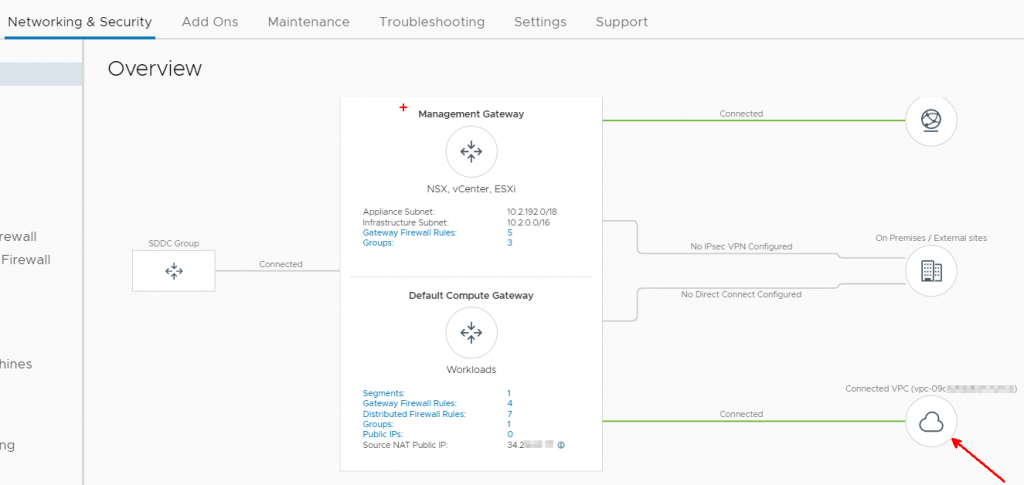
I first wanted to build a domain controller in the connected VPC, allowing AD communication across the ENI. If you already have a domain controller accessible via VPN or Direct Connect, you do not need to worry about this part of the configuration, you can skip to Step 2. But I wanted to demonstrate AD communication across the ENI as part of this post. To figure out which EC2 subnet I need my domain controller in, I looked at Networking & Security Overview
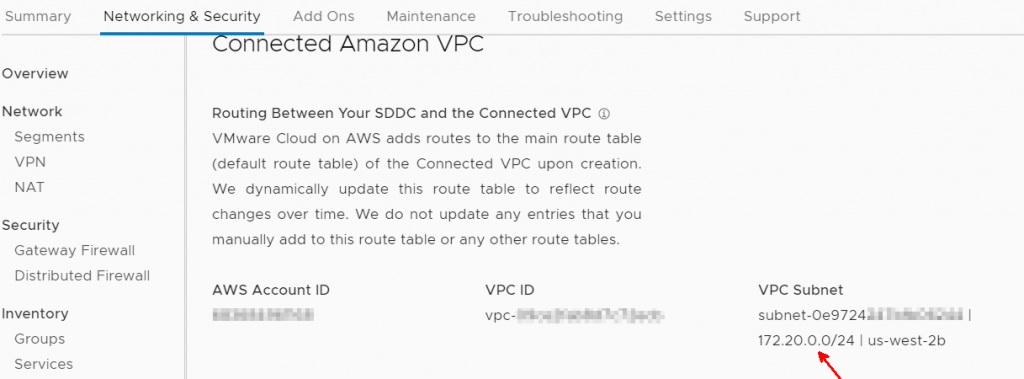
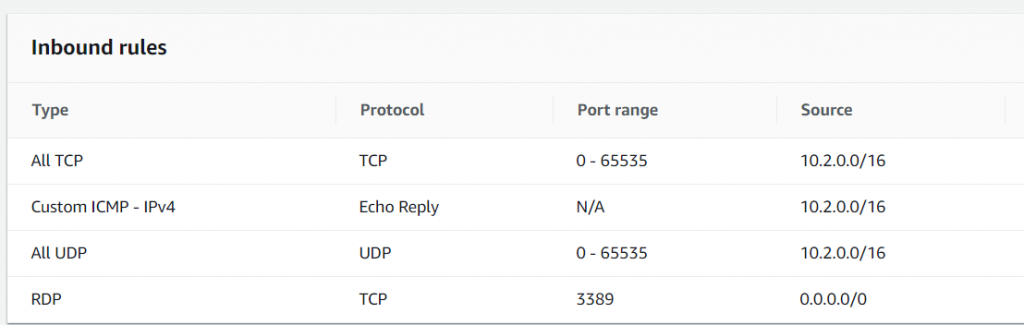
I created a Windows 2016 EC2 instance, gave it an IP of 172.20.0.249, and promoted it to a domain controller. My test domain was named: poc.test. I needed to open the firewall to allow the management network in VMC to communicate with the domain controller. Best practice would obviously be to restrict communication to only Active Directory ports, but I opened it all up to make things simpler. The 0.0.0.0/0 for RDP was to allow domain controller access from the public internet – obviously not something you’d want to do in production, but this is just a temporary lab. The default outbound rule in EC2 is to allow everything, which I left in place.
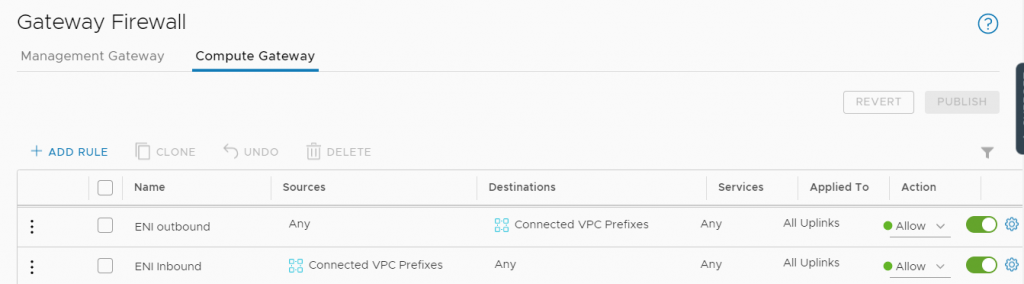
I also needed to open the compute gateway firewall to allow bidirectional communication across the ENI, which I’ve done below.
Step 2
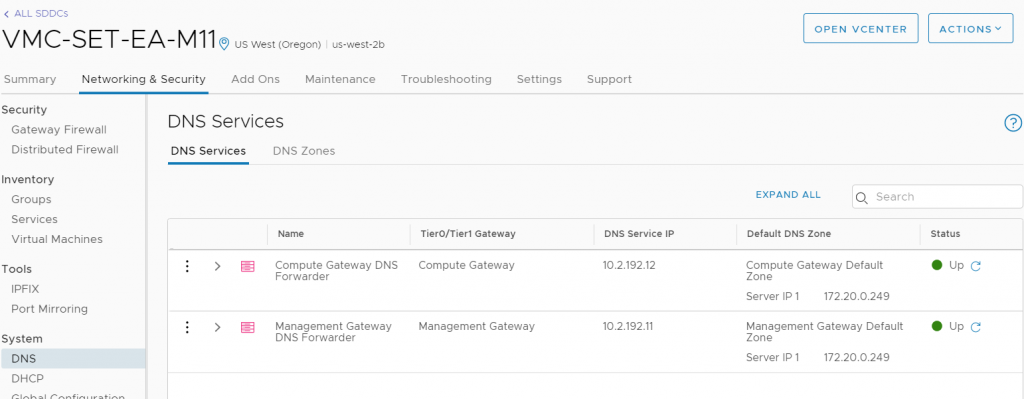
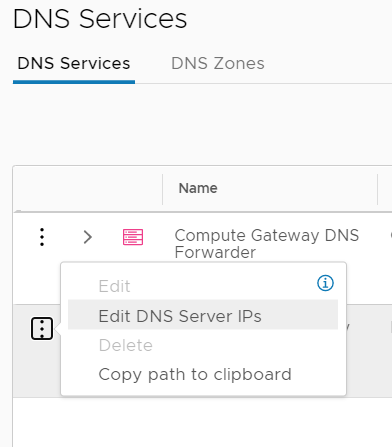
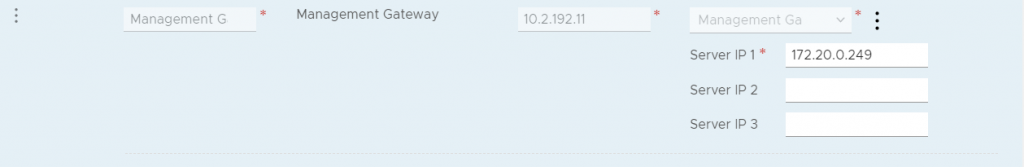
Once you have a Domain Controller available, you need to point the management gateway DNS to your domain controller. In this example I also pointed the Compute Gateway DNS to the domain controller.
Step 3
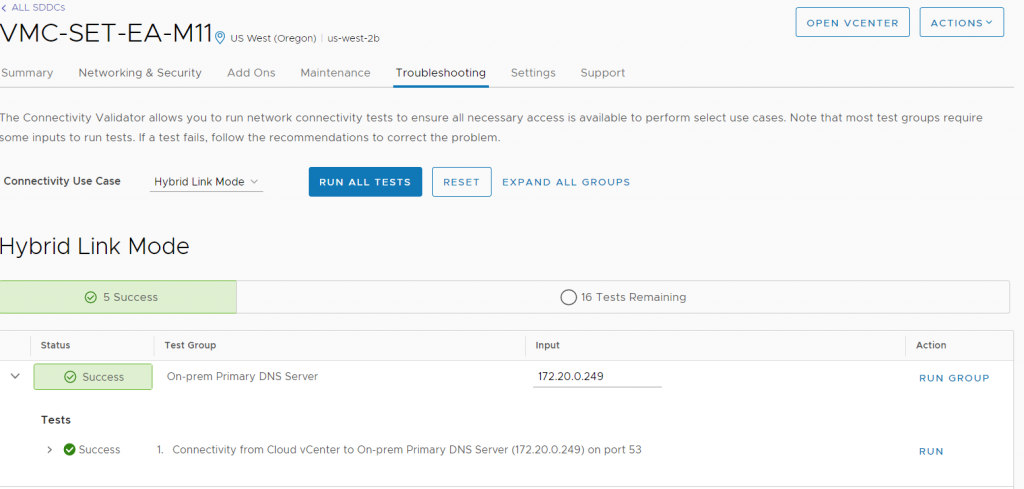
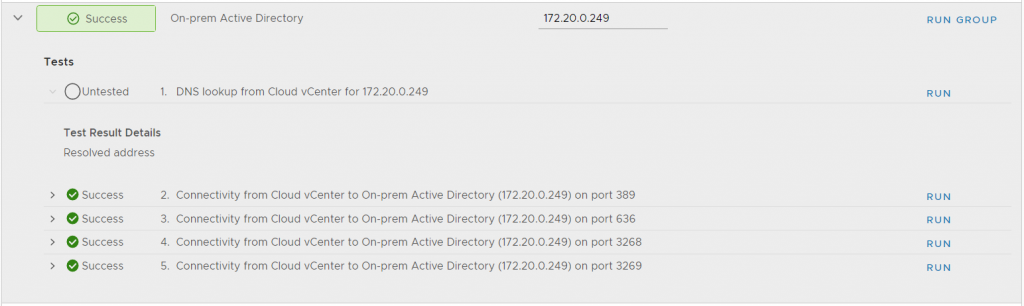
Even though you’re not setting up Hybrid Linked Mode, it’s a good idea to use some of the HLM troubleshooting tools to ensure connectivity to the domain controller. I ran the 5 tests shown below against my DC IP 172.20.0.249
Step 4
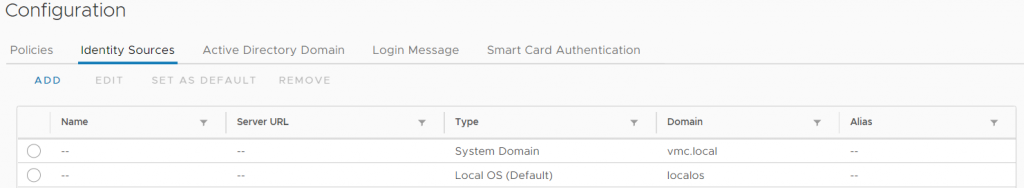
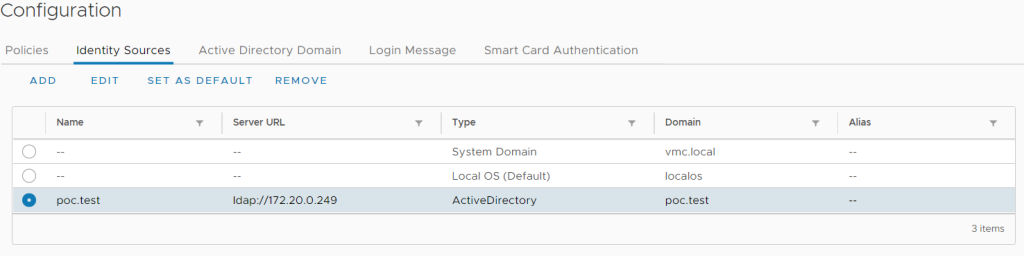
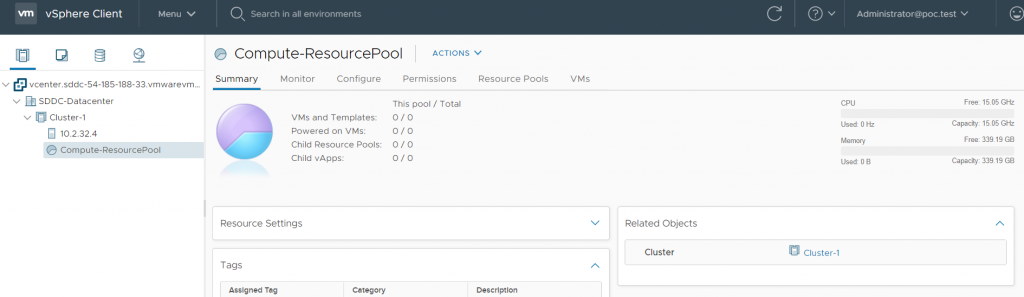
Now we need to configure an identity source in the VMC vCenter. Log in as cloudadmin@vmc.local. You can find this under Menu>Administration, then Single Sign On>Configuration, then Identity Sources. Click Add to add an identity source.
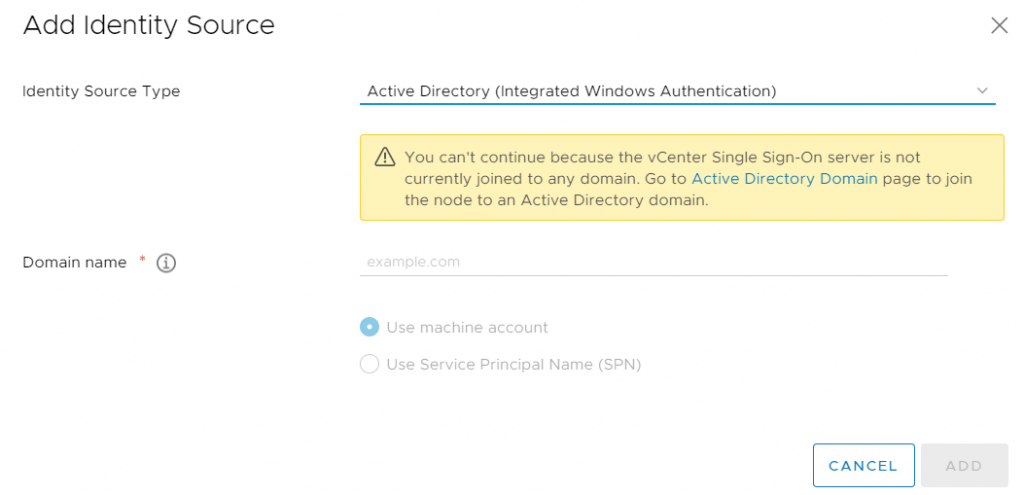
Select Active Directory over LDAP in the Identity Source Type dropdown.
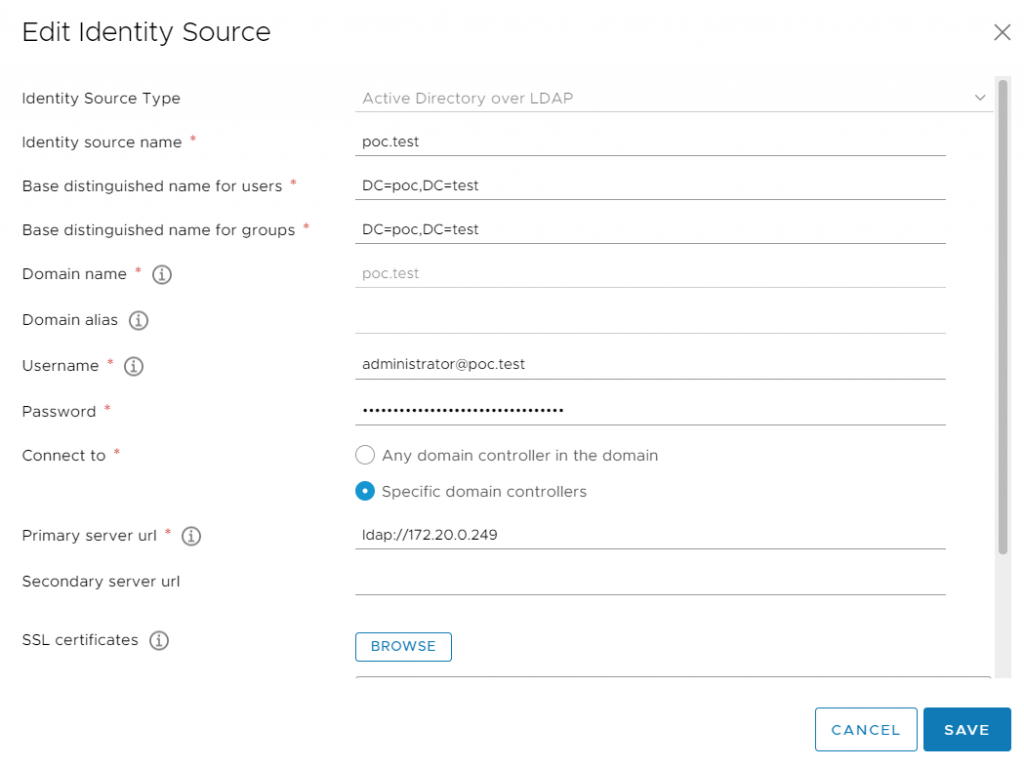
Fill out the identity source according to your Active Directory environment. You would want to use the secondary LDAP server in production, and you would never use a Domain Admin account as the LDAP user in production.
Once the identity source is added, you will see it in the list.
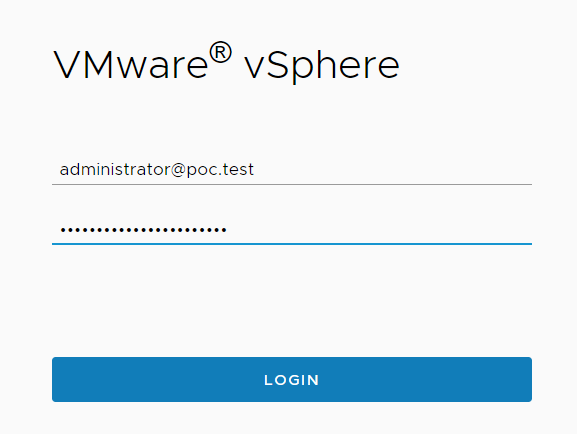
Log out as cloudadmin@vmc.local and log in as a domain user.
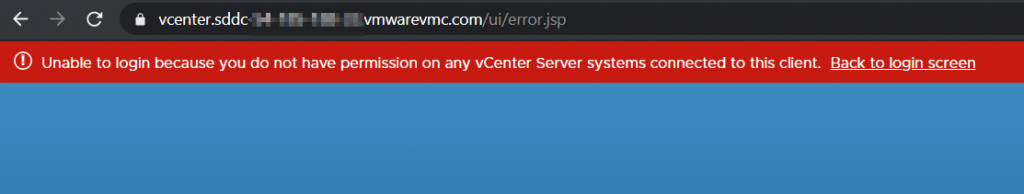
If we enter the correct password, we receive this error. This is OK as we have not granted any domain user access to our vCenter. All domain users are granted No Access by default.
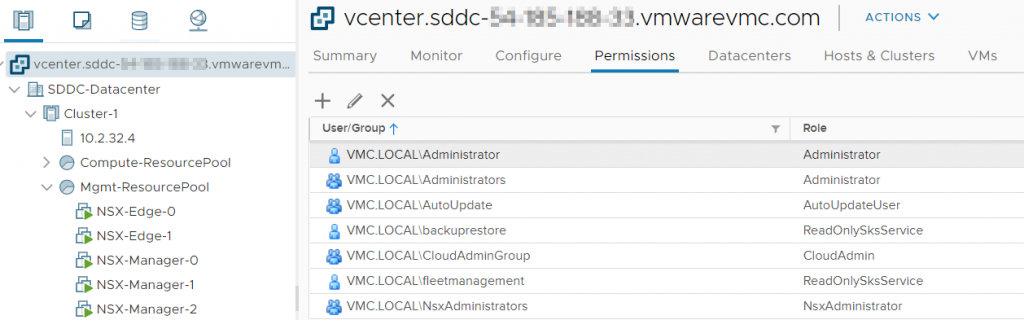
Log back in as cloudadmin and grant privileges to a domain user. In our case we want to grant admin rights at the vCenter level, we click on the vCenter object, then Permissions, then the plus to add a permission.
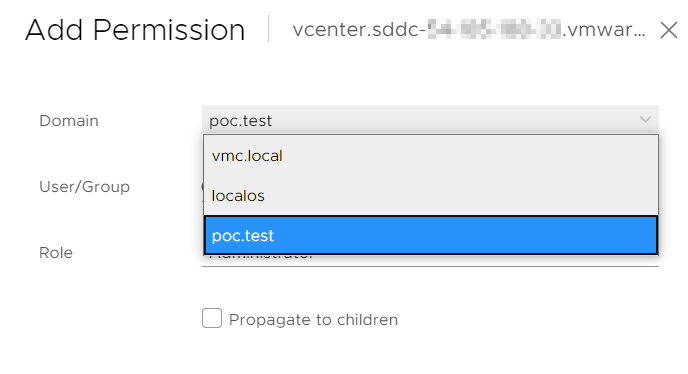
The AD domain should show up in the dropdown.
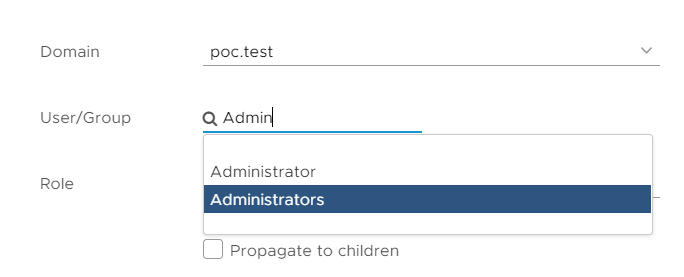
If you start typing in the User/Group line, a dropdown will auto-populate with matching AD objects. I pick Administrators.
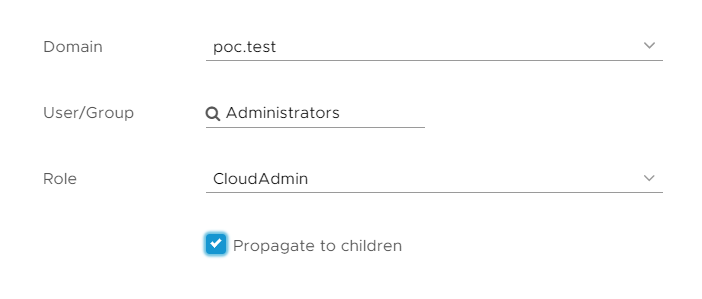
Be careful here – you cannot grant the Administrator role in VMC because you are not an administrator – only VMware support has full administrative access to an SDDC. Instead, grant the CloudAdmin role. Check Propogate to send the permission down the entire tree.
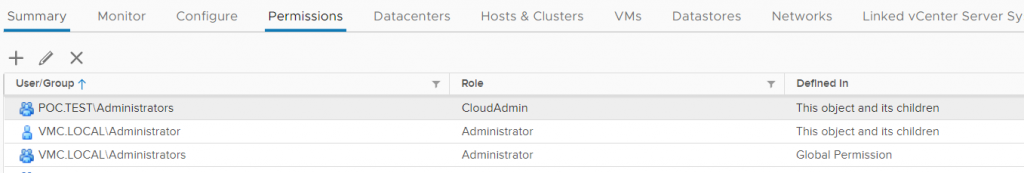
We now see the new permission in the Permissions list.
Now log off as cloudadmin, and log in as the AD user.
Success! You can now grant permissions to Active Directory users.

Singh
Hello
Great post and much needed one. If we are using the on-prem DCs, what ports are required for the AD Identity SSO to work using LDAPS.
1. 636 for LDAPS
2. 53 TCP/UDP DNS
3. 88 for Kerberos Authentication ?
Any other? Appreciate the help.
Thank you
pkremer
You can use the Hybrid Linked mode tests in the Troubleshooting section to your advantage, it shows ports for DNS, LDAP, and GC