In this AWS re:Post Article, I describe the purpose behind IN, OUT, and IN_OUT rules, with examples
Tag: NSX
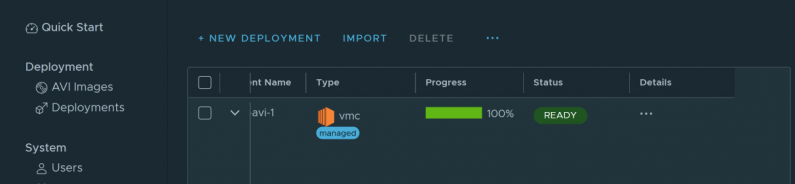
NSX Advanced Load Balancer – Part V – Application VIP Assignments
In Part I, we assigned the application VIPs a range out of the back half of the 10.47.165.0/24 subnet. This […]
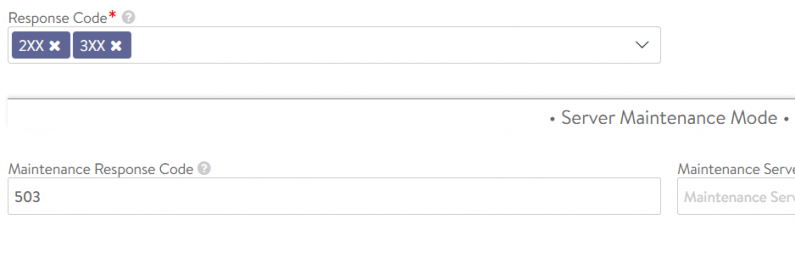
NSX Advanced Load Balancer – Part IV – Health Check Maintenance Mode
In Part III of this series, we looked active health monitors for the sample web application created by Easy Deploy. […]
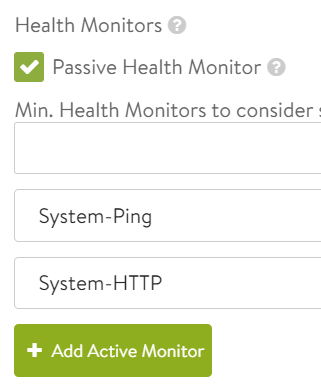
NSX Advanced Load Balancer – Part III – Active HTTP Monitor
In Part II of this series, we looked at some of the resources that Easy Deploy built for us, including […]
NSX Advanced Load Balancer – Part II – Examining the Easy Deploy Resources
In Part I of this series, we deployed NSX Advanced Load Balancer resources with the Easy Deploy Fling. In this […]
NSX per-VM licensing compliance
I had a customer with a production cluster of around 100 VMs. They needed to segment off a few VMs due […]
My VMware VCP-NV certification experience
I’ve created a new VCP-NV page with details on how I passed the VCP-NV exam today!
A quick NSX microsegmentation example
This short post demonstrates the power of NSX. My example is a DMZ full of webservers – you don’t want […]