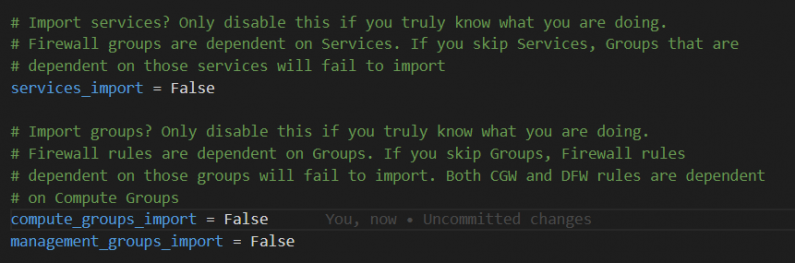
The Fling runs import commands serially – this can result in an extremely long import time for customers with large […]
Run Kubernetes locally in minutes with Tanzu Community Edition
I became aware of this post less than an hour ago (currently 4PM CDT on May 10th). It describes how […]
Invoke-GetVMGuestLocalFilesystem displays no data
I had a customer report the following in VMware {Code} Slack: Hello! I’m trying to automate the increment of disk […]
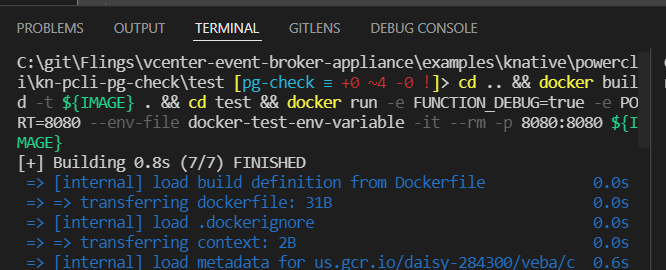
VMware Event Broker Appliance – Part X – Building a New PowerCLI Function – Function Deployment
In the previous post, I walked line-by-line through the code that comprises the kn-pcli-pg-check example function. In this post, we […]
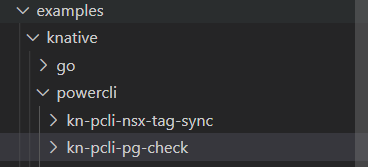
VMware Event Broker Appliance – Part IX – Building a New PowerCLI Function – Writing Code
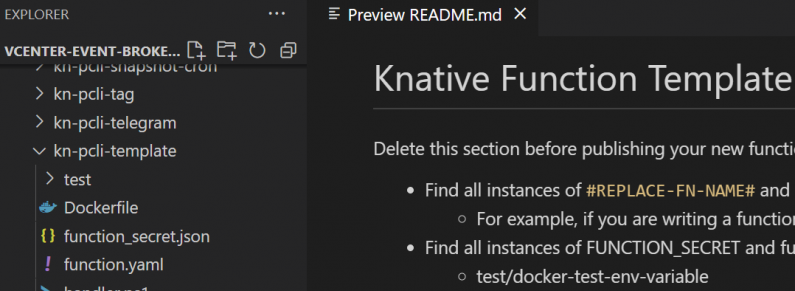
In Part VIII, we prepared to write code for a new PowerCLI function using the PowerCLI template. In this post, […]
VMware Event Broker Appliance – Part VIII – Building a New PowerCLI Function – Preparation
In the previous post, we discussed Let’s Encrypt public certificates in VEBA. In the next few posts, we will discuss […]
New Year, New (Temporary) Role
The Take3 program lets a VMware employee with five or more years of service take a three month rejuvenation period […]
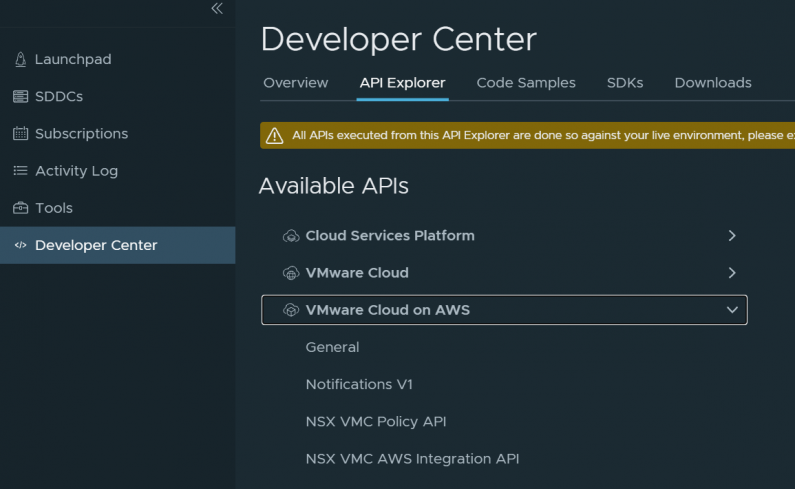
SDDC Import/Export for VMware Cloud on AWS – Part VIII – API Pagination
Building a Fling One of the fun things working for VMware is that anybody can create a Fling. If you […]
VMware Cloud on AWS Showback with vRealize Operations Manager
I had a customer ask me what options we have for chargeback/showback for VMs in VMware Cloud on AWS. vRealize […]
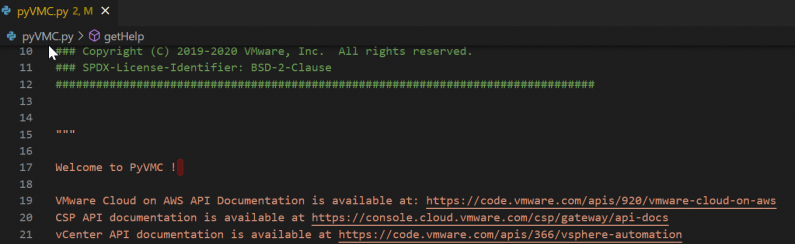
Python Client for VMC on AWS – Part II – More User Management
In Part I of this series, we examined some of the user management functions in v1.4 of PyVMC. In this […]